HOW TO PROTECT PATIENT DATA IN CONNECTED DEVICES: A COMPREHENSIVE GUIDE TO MEDICAL DEVICE DATA PRIVACY AND SECURITY

The rapid evolution of connected medical devices has revolutionized healthcare delivery, enabling real-time patient monitoring, personalized treatment plans, and seamless data integration across healthcare systems. However, this digital transformation brings unprecedented cybersecurity challenges that threaten patient privacy and data security. As healthcare organizations increasingly rely on Internet of Things (IoT) medical devices, protecting sensitive patient information has become a critical priority that demands comprehensive security strategies and robust compliance frameworks.
The Connected Healthcare Landscape: Opportunities and Vulnerabilities
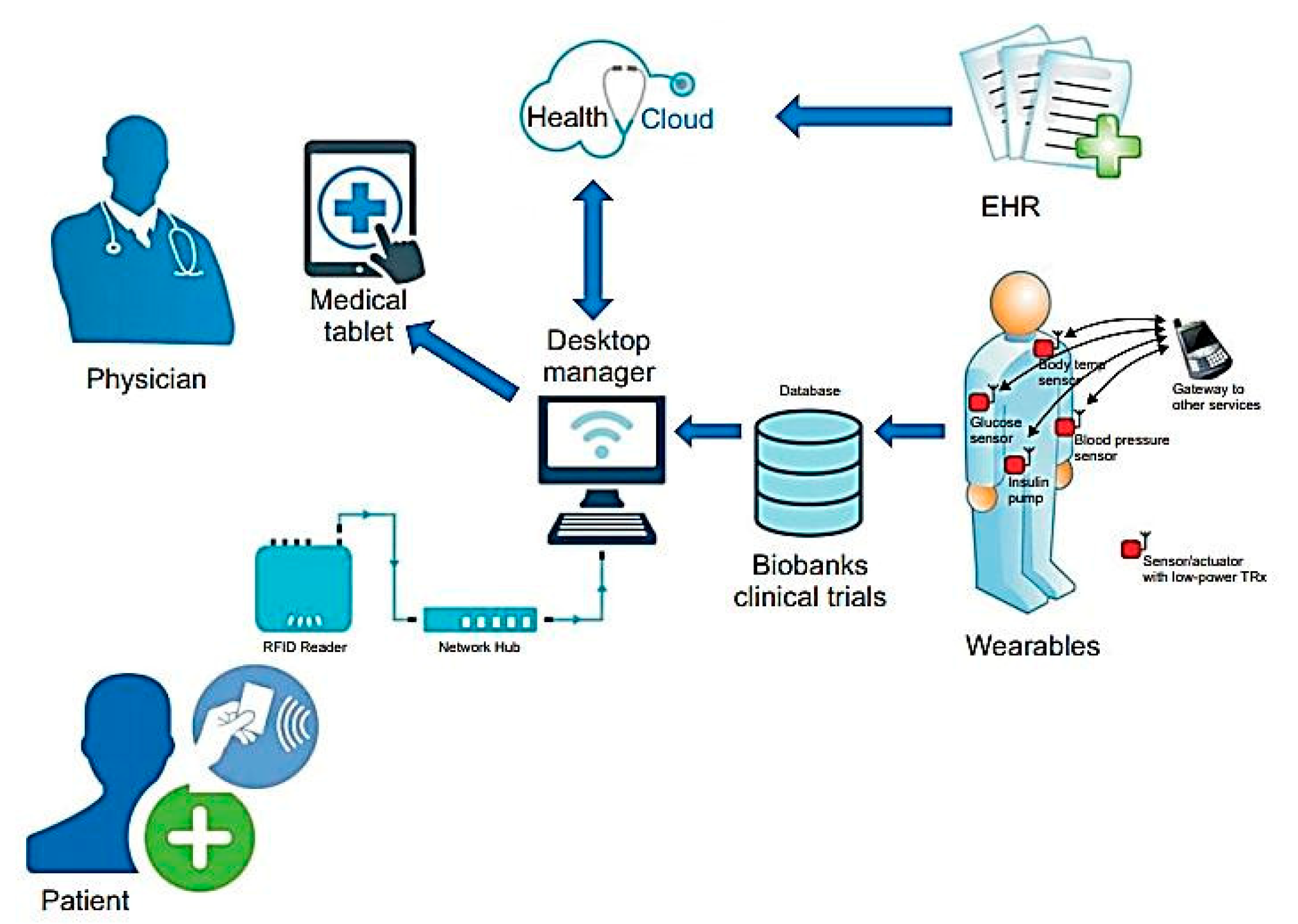
The healthcare IoT ecosystem encompasses a vast network of interconnected devices, from wearable fitness trackers and glucose monitors to sophisticated implantable cardiac devices and hospital-grade monitoring systems. According to recent cybersecurity research, these devices often collect, store, and transmit protected health information (PHI) across mobile applications, cloud platforms, and provider systems, creating complex security challenges that extend far beyond traditional IT infrastructure.
The Scale of Connected Medical Device Adoption
The proliferation of connected medical devices has created an expansive attack surface that cybercriminals increasingly target. Modern healthcare facilities typically deploy hundreds of connected devices, each representing a potential entry point for malicious actors. These devices range from:
- Patient Monitoring Systems: Continuous vital sign monitors, cardiac telemetry units, and respiratory monitoring devices
- Therapeutic Devices: Smart insulin pumps, connected pacemakers, and automated medication dispensers
- Diagnostic Equipment: Portable ultrasound machines, connected X-ray systems, and point-of-care testing devices
- Wearable Health Technology: Fitness trackers, smartwatches, and continuous glucose monitors
Data Flow Complexity
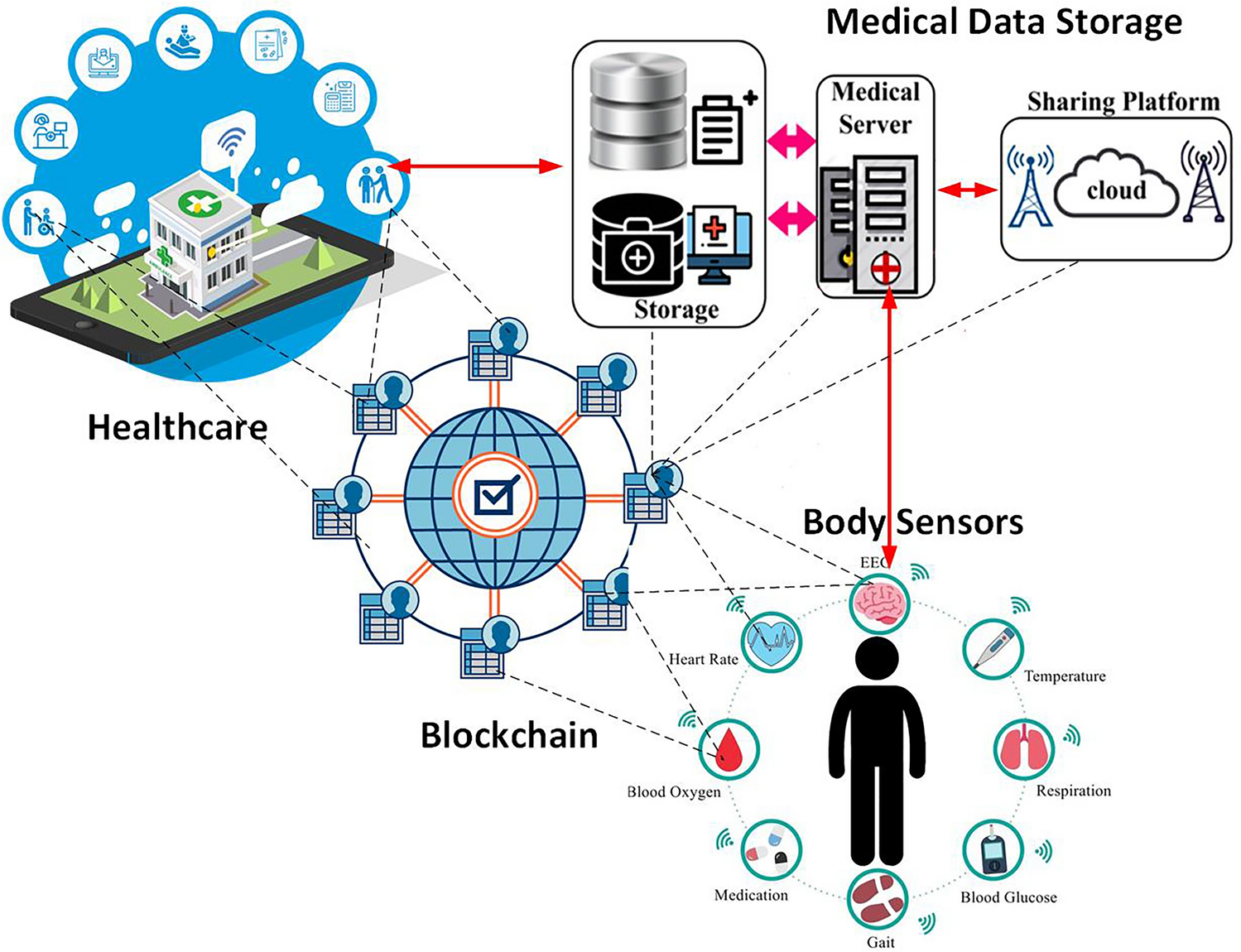
Connected medical devices create complex data ecosystems where patient information flows through multiple touchpoints. A single glucose reading from a continuous monitor might travel through:
- Device sensors collecting physiological data
- Bluetooth Low Energy (BLE) transmission to mobile applications
- Mobile applications processing and displaying information
- Cloud storage platforms maintaining historical data
- Electronic Health Record (EHR) systems integrating with clinical workflows
- Healthcare provider networks enabling clinical decision-making
Each connection point represents a potential vulnerability that must be secured through comprehensive cybersecurity measures.
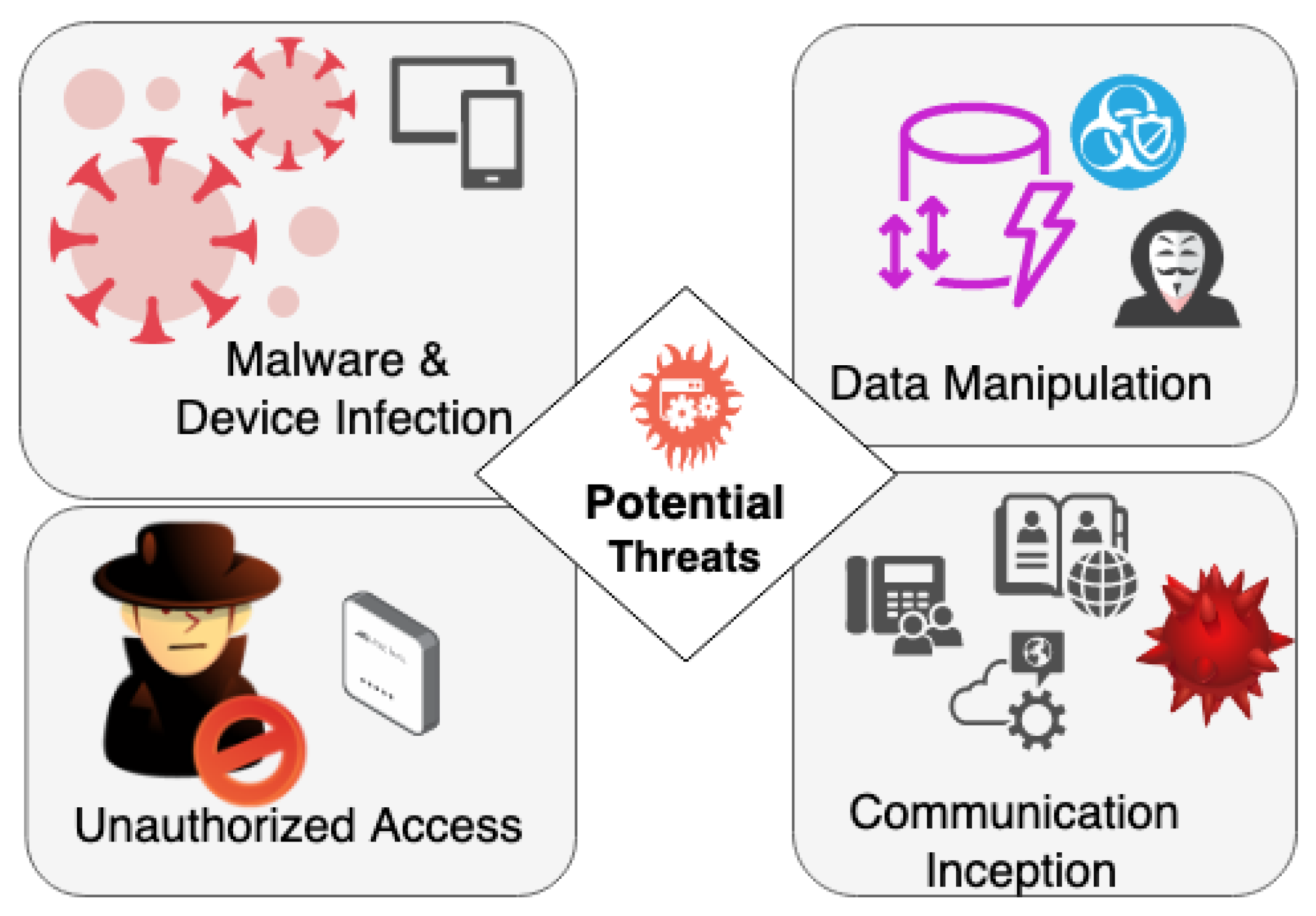
Major Cybersecurity Threats in Connected Healthcare

Understanding the threat landscape is essential for developing effective protection strategies. Healthcare cybersecurity faces unique challenges due to the life-critical nature of medical devices and the sensitive nature of patient data.
Man-in-the-Middle (MITM) Attacks
One of the most prevalent threats to connected medical devices involves intercepting communications between devices and their paired applications or cloud backends. MITM attacks typically target:
- Unsecured Bluetooth connections between devices and mobile applications
- Wi-Fi communications in healthcare facilities with inadequate network security
- API communications between applications and cloud services
- Firmware update processes that lack proper encryption and authentication
Ransomware and Healthcare Network Infiltration

Ransomware attacks pose significant threats to healthcare operations, particularly when attackers gain access through poorly secured IoT devices. Recent security research reveals that 39% of nurse call systems had unpatched critical vulnerabilities, while 48% had other security issues that could facilitate network infiltration.
Firmware and Software Exploitation
Connected medical devices often contain vulnerabilities in their firmware or software that can be exploited for:
- Remote code execution enabling unauthorized device control
- Data exfiltration compromising patient privacy
- Device manipulation potentially affecting patient safety
- Network lateral movement spreading attacks across healthcare systems
Insider Threats and Access Control Failures
Not all cybersecurity threats originate from external sources. Internal risks include:
- Privileged user account abuse by healthcare staff with excessive system access
- Misconfigured access controls allowing unauthorized data access
- Social engineering attacks targeting healthcare personnel
- Physical device tampering in unsecured healthcare environments
Regulatory Compliance Framework
Protecting patient data in connected medical devices requires adherence to comprehensive regulatory frameworks designed to ensure both patient safety and data privacy.
FDA Cybersecurity Requirements
The U.S. Food and Drug Administration (FDA) has established stringent cybersecurity requirements for medical device manufacturers that must be integrated throughout the product lifecycle.
Pre-Market Security Requirements
FDA cybersecurity guidelines mandate that manufacturers demonstrate comprehensive security planning before market approval:
- Threat Modeling and Risk Assessment: Systematic identification of potential cybersecurity risks and vulnerabilities
- Secure Software Design: Implementation of security controls throughout the software development lifecycle
- Trust Boundary Documentation: Clear definition of security perimeters and data flow controls
- Cybersecurity Labeling: Comprehensive documentation for users and IT professionals regarding security features and requirements
Post-Market Surveillance Obligations
Following device deployment, manufacturers must maintain ongoing cybersecurity vigilance:
- Vulnerability Management Programs: Systematic processes for identifying, assessing, and addressing security vulnerabilities
- Coordinated Disclosure Policies: Formal procedures for receiving and responding to security vulnerability reports
- Software Update Mechanisms: Secure processes for distributing security patches and firmware updates
- Incident Response Capabilities: Comprehensive plans for responding to cybersecurity incidents
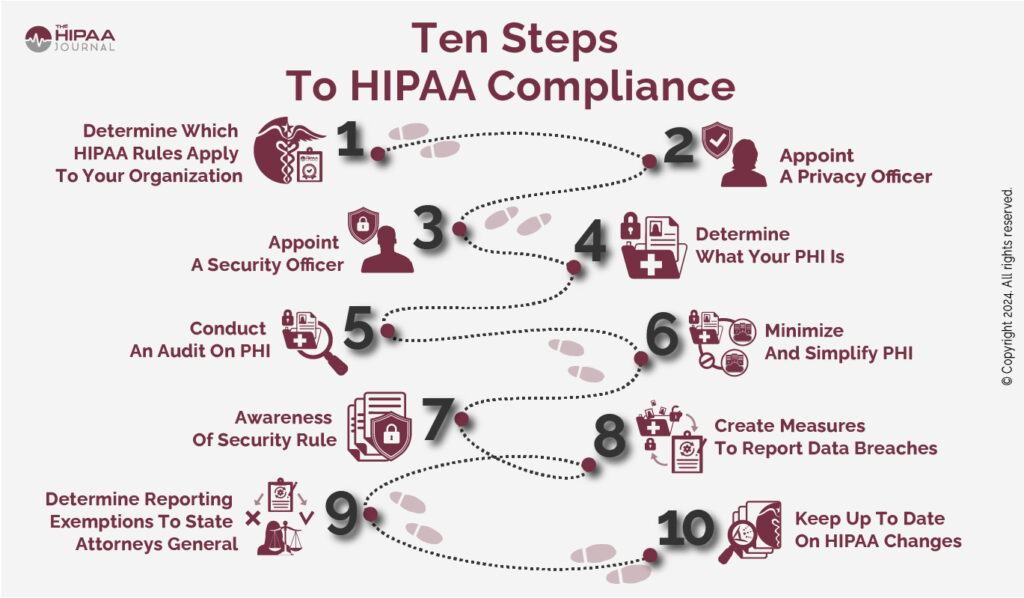
HIPAA Compliance for Connected Devices

The Health Insurance Portability and Accountability Act (HIPAA) establishes critical privacy and security requirements for protecting patient health information in connected medical devices.
Protected Health Information (PHI) Safeguards
HIPAA requires comprehensive protection for electronically stored and transmitted PHI:
- Administrative Safeguards: Policies and procedures governing workforce access to PHI
- Physical Safeguards: Controls protecting physical access to systems and workstations
- Technical Safeguards: Technology-based protections for electronic PHI access and transmission
Business Associate Agreements
Healthcare organizations must establish formal agreements with technology vendors handling PHI, ensuring:
- Contractual security obligations for all parties handling patient data
- Incident notification requirements for potential data breaches
- Data handling and disposal procedures protecting PHI throughout its lifecycle
International Standards and Frameworks

Global medical device cybersecurity relies on internationally recognized standards:
- IEC 62304: Software lifecycle processes for medical device software
- ISO 27001: Information security management systems requirements
- IEC 81001-5-1: Health software and health IT systems cybersecurity requirements
- NIST Cybersecurity Framework: Comprehensive approach to managing cybersecurity risks
Technical Security Implementation Strategies
Implementing robust technical security measures requires a comprehensive approach addressing all aspects of connected medical device ecosystems.
Data Encryption and Protection
Comprehensive data protection forms the foundation of medical device cybersecurity:
Encryption in Transit
- End-to-end encryption for all device communications using industry-standard protocols (TLS 1.3, AES-256)
- Certificate-based authentication ensuring communication partner verification
- Perfect Forward Secrecy protecting past communications even if long-term keys are compromised
Encryption at Rest
- Database encryption protecting stored patient data using advanced encryption standards
- File system encryption securing data stored on device and system storage
- Key management systems ensuring secure encryption key generation, distribution, and rotation

Secure Device Authentication and Access Control
Robust authentication mechanisms prevent unauthorized access to medical devices and patient data:
Multi-Factor Authentication (MFA)
- Healthcare provider authentication requiring multiple verification factors
- Device authentication ensuring only authorized devices access healthcare networks
- Patient identity verification protecting access to personal health information
Role-Based Access Control (RBAC)
- Principle of least privilege ensuring users access only necessary data and functions
- Granular permissions controlling specific actions and data access levels
- Regular access reviews maintaining appropriate authorization levels
Network Security Architecture

Comprehensive network security protects connected medical devices from various attack vectors:
Network Segmentation
- Medical device isolation separating IoT devices from general network traffic
- Virtual LANs (VLANs) creating secure network segments for different device types
- Microsegmentation implementing granular network access controls
Intrusion Detection and Prevention
- Real-time monitoring detecting unusual network activity and potential threats
- Automated response systems immediately addressing identified security incidents
- Behavioral analytics identifying anomalous device and user behavior patterns
Firmware and Software Security
Securing device software and firmware prevents exploitation of vulnerabilities:
Secure Boot Processes
- Cryptographic verification ensuring only authenticated firmware executes on devices
- Hardware security modules providing tamper-resistant security functions
- Chain of trust maintaining security from device startup through operation
Over-the-Air (OTA) Update Security
- Encrypted update packages protecting firmware updates during transmission
- Digital signatures verifying update authenticity and integrity
- Rollback capabilities enabling recovery from problematic updates
Zero Trust Security Architecture for Healthcare IoT
![]()
Implementing Zero Trust architecture provides comprehensive security for connected medical device ecosystems by eliminating implicit trust and continuously validating all access requests.
Core Zero Trust Principles
Never Trust, Always Verify
- Continuous authentication for all users, devices, and applications
- Real-time authorization validating access requests based on current context
- Dynamic risk assessment adjusting security measures based on threat levels
Least Privilege Access
- Minimal access rights providing only necessary permissions for specific tasks
- Time-based access limiting access duration to reduce exposure windows
- Contextual access controls adjusting permissions based on user location, device, and behavior
Implementation Strategies
Device Identity and Trust
- Unique device certificates providing cryptographic identity for each connected device
- Device attestation continuously verifying device integrity and authenticity
- Trust scoring dynamically assessing device trustworthiness based on behavior and security posture
Data-Centric Security
- Information-centric protection securing data regardless of location or access method
- Dynamic data classification automatically categorizing data based on sensitivity and context
- Data loss prevention preventing unauthorized data access and exfiltration
Compliance Monitoring and Incident Response

Continuous monitoring and rapid incident response capabilities ensure ongoing security and compliance in connected healthcare environments.
Security Monitoring and Analytics
Real-Time Threat Detection
- Security Information and Event Management (SIEM) systems aggregating and analyzing security events
- Machine learning algorithms identifying patterns indicative of security threats
- Automated alerting notifying security teams of potential incidents requiring immediate attention
Vulnerability Management
- Continuous scanning identifying security vulnerabilities in connected devices and systems
- Risk-based prioritization focusing remediation efforts on highest-risk vulnerabilities
- Patch management systematically applying security updates across device ecosystems
Incident Response Framework
Preparation and Planning
- Incident response team establishing dedicated personnel with defined roles and responsibilities
- Response procedures documenting step-by-step incident handling processes
- Communication plans ensuring appropriate stakeholder notification during incidents
Detection and Analysis
- Incident classification categorizing security events based on severity and impact
- Forensic capabilities preserving and analyzing digital evidence
- Impact assessment determining the scope and consequences of security incidents
Containment and Recovery
- Immediate containment isolating affected systems to prevent incident spread
- System restoration recovering normal operations while maintaining security
- Lessons learned incorporating incident insights into improved security measures
Best Practices for Healthcare Organizations

Implementing comprehensive patient data protection requires organizational commitment to security best practices across all levels of healthcare operations.
Organizational Security Culture
Leadership Commitment
- Executive sponsorship ensuring adequate resources and attention for cybersecurity initiatives
- Board oversight providing governance and accountability for security programs
- Clear policies establishing organizational expectations for data protection and security
Staff Training and Awareness
- Regular security training educating healthcare personnel about cybersecurity threats and best practices
- Phishing simulation testing and improving staff ability to recognize social engineering attacks
- Incident reporting encouraging staff to report potential security issues without fear of retribution
Device Lifecycle Management
Procurement and Deployment
- Security requirements including cybersecurity specifications in device procurement processes
- Security testing validating device security before deployment in clinical environments
- Configuration management ensuring devices are securely configured before patient use
Ongoing Maintenance
- Regular updates maintaining current security patches and software versions
- Performance monitoring tracking device performance and security metrics
- End-of-life planning securely decommissioning devices and protecting residual data
Vendor Risk Management

Managing third-party vendor relationships critical for connected device security:
Due Diligence Processes
- Security assessments evaluating vendor cybersecurity capabilities and practices
- Contractual requirements including specific security obligations in vendor agreements
- Ongoing monitoring continuously assessing vendor security posture and performance
Supply Chain Security
- Component verification ensuring security of device hardware and software components
- Trusted suppliers working with vendors demonstrating strong security practices
- Supply chain transparency understanding the complete device manufacturing and distribution process
Emerging Technologies and Future Considerations
The future of connected medical device security will be shaped by emerging technologies and evolving threat landscapes that require proactive planning and adaptation.
Artificial Intelligence and Machine Learning
AI-Powered Security Analytics
- Predictive threat intelligence using machine learning to anticipate and prevent cyberattacks
- Behavioral analysis identifying anomalous device and user behavior patterns
- Automated response implementing AI-driven incident response and threat mitigation
Privacy-Preserving AI
- Federated learning training AI models without centralizing sensitive patient data
- Differential privacy adding mathematical privacy guarantees to data analysis
- Homomorphic encryption enabling computation on encrypted data without decryption
Blockchain and Distributed Security
Decentralized Identity Management
- Self-sovereign identity giving patients control over their health data sharing
- Immutable audit trails creating tamper-proof records of data access and sharing
- Smart contracts automating compliance and access control processes
Quantum Computing Implications
Post-Quantum Cryptography
- Quantum-resistant algorithms preparing for future quantum computing threats to current encryption methods
- Cryptographic agility enabling rapid adoption of new security algorithms as needed
- Long-term data protection ensuring patient data remains secure against future technological advances
Implementation Roadmap and Recommendations
Successfully protecting patient data in connected medical devices requires a systematic approach that addresses technical, organizational, and regulatory requirements.
Phase 1: Assessment and Planning (Months 1-3)
Current State Analysis
- Asset inventory cataloging all connected medical devices and associated systems
- Risk assessment identifying cybersecurity vulnerabilities and potential threats
- Gap analysis comparing current security measures against regulatory requirements and best practices
Strategic Planning
- Security roadmap developing a comprehensive plan for addressing identified gaps
- Budget allocation securing necessary resources for security improvements
- Stakeholder engagement obtaining organizational commitment and support
Phase 2: Foundation Building (Months 4-9)
Technical Infrastructure
- Network segmentation implementing secure network architecture for medical devices
- Identity management deploying comprehensive authentication and access control systems
- Monitoring capabilities establishing security monitoring and incident response systems
Policy and Governance
- Security policies developing comprehensive cybersecurity policies and procedures
- Training programs implementing ongoing security awareness and education initiatives
- Vendor management establishing security requirements for third-party partners
Phase 3: Advanced Security Measures (Months 10-18)
Zero Trust Implementation
- Microsegmentation implementing granular network access controls
- Continuous verification deploying advanced authentication and authorization systems
- Data protection implementing comprehensive encryption and data loss prevention measures
Advanced Analytics
- AI-powered monitoring deploying machine learning-based threat detection systems
- Predictive analytics implementing proactive threat intelligence capabilities
- Automated response establishing automated incident response and remediation processes
Phase 4: Continuous Improvement (Ongoing)
Regular Assessment
- Security audits conducting periodic comprehensive security assessments
- Penetration testing regularly testing security measures against simulated attacks
- Compliance monitoring ensuring ongoing adherence to regulatory requirements
Evolution and Adaptation
- Threat intelligence staying current with emerging cybersecurity threats and attack methods
- Technology updates adopting new security technologies and best practices
- Regulatory compliance maintaining compliance with evolving regulatory requirements
Conclusion: Building a Secure Connected Healthcare Future

The protection of patient data in connected medical devices represents one of the most critical challenges facing modern healthcare. As the industry continues to embrace digital transformation and IoT integration, the complexity and sophistication of cybersecurity threats will only increase. However, by implementing comprehensive security frameworks, adhering to regulatory requirements, and fostering a culture of security awareness, healthcare organizations can successfully navigate these challenges while realizing the tremendous benefits of connected medical technology.
The key to success lies in recognizing that cybersecurity is not merely a technical challenge but a fundamental aspect of patient safety and care quality. Organizations that prioritize data protection, invest in robust security measures, and maintain vigilant monitoring and response capabilities will be best positioned to deliver safe, effective, and trustworthy connected healthcare services.
As we look toward the future, emerging technologies such as artificial intelligence, blockchain, and quantum computing will create new opportunities for enhancing medical device security while also introducing novel challenges that must be proactively addressed. Healthcare organizations that begin building comprehensive security foundations today will be best prepared to adapt and thrive in tomorrow’s increasingly connected healthcare landscape.
The investment in protecting patient data through comprehensive cybersecurity measures is not just a regulatory requirement or business necessity—it is a moral imperative that ensures the trust and safety of the patients we serve. By embracing this responsibility and implementing the strategies outlined in this guide, healthcare organizations can confidently pursue the promise of connected medical technology while safeguarding the most precious asset in healthcare: patient trust and data privacy.
The future of healthcare depends on our collective ability to innovate securely, and the time to act is now. Through careful planning, strategic implementation, and ongoing vigilance, we can build a connected healthcare ecosystem that delivers unprecedented clinical benefits while maintaining the highest standards of patient data protection and privacy.